Software patches are a critical security practice in today’s fast-moving digital environment that organizations cannot ignore, especially as threats evolve and regulations tighten. They fix vulnerabilities, close security gaps, and help prevent disruptions caused by bugs and compatibility issues in complex, heterogeneous environments. Yet many teams struggle to move from reactive patching to proactive patch management best practices in large, distributed IT estates and multi-cloud landscapes. This guide explains why updates matter and offers practical steps on how to manage patches effectively, with attention to patching cadence and schedules. With the right mix of visibility, automation, and governance, organizations can improve security, compliance, and operational resilience.
Beyond the term patches, organizations often speak of updates, fixes, or security releases that seal vulnerabilities before they can be exploited. This lifecycle of updates connects to vulnerability remediation, software maintenance, and version control, helping keep platforms compatible and compliant. Thinking in terms of patches, updates, and security advisories allows teams to map a structured cadence, assign ownership, and monitor progress across on-premises, cloud, and hybrid environments, including automated software updates. Together, these approaches reduce exposure, downtime, and risk, while supporting a resilient and compliant IT landscape.
Understanding Patch Management: What It Is and Why It Matters
Patch management is the ongoing discipline of identifying, testing, and deploying software updates across all assets to mitigate vulnerabilities and improve reliability. It links security, operations, and governance by ensuring that known weaknesses are addressed before they can be exploited. In practice, it means maintaining visibility into what runs in the environment, prioritizing fixes, and coordinating changes with minimal business disruption.
The importance of software updates goes beyond protection from exploits. Following patch management best practices helps reduce risk, maintain compatibility, and stabilize performance across endpoints, servers, and cloud workloads. When teams treat patches as a strategic security control rather than a one-off task, they lay the groundwork for faster response to new threats and better outcomes for compliance and audits.
The Patch Management Lifecycle: From Inventory to Verification
A successful program starts with a clear lifecycle that guides when and how patches are applied. Begin with inventory and classification to know what is at risk, including operating systems, applications, drivers, and firmware. Accurate asset visibility is the foundation of consistent patching and helps reveal gaps before exploitation.
Next comes vulnerability assessment, testing and staging, controlled deployment, and verification. This sequence helps you prioritize high-severity fixes, validate compatibility, and maintain an auditable trail. Governance and rollback planning further reduce risk by ensuring you can reverse changes quickly if issues arise.
Establishing a Patching Cadence and Schedules That Work
A predictable cadence accelerates decision-making and reduces firefighting. Define a regular patching window (for example, monthly releases) and assign ownership to schedule testing, deployment, and validation. A disciplined cadence makes it easier to coordinate across security, IT, and development teams while keeping downtime and disruption manageable.
Include a clear path for critical or zero-day patches within the cadence. This ensures urgent Software patches are addressed promptly without derailing routine maintenance. The cadence and scheduling approach supports proactive risk reduction rather than reactive patching.
Automating Discovery, Testing, and Deployment: Tools That Scale Patch Management
Automation accelerates discovery, testing, deployment, and reporting. Modern environments benefit from continuous software inventory and policy-driven patch detection, reducing manual toil and helping teams see gaps earlier. Automated processes also enable faster feedback and tighter control over release quality.
When you implement automated software updates, pair them with safeguards such as pre-deployment checks, automated rollback, and approvals for critical systems. This balance preserves speed while maintaining governance and reducing the risk of unintended consequences.
Measuring Compliance and Security Outcomes with Patch Management Best Practices
To prove value, measure patch coverage, time-to-patch, and residual risk. Dashboards and reports translate technical activity into business impact, helping leaders understand how patching reduces exposure and strengthens resilience.
Adopting patch management best practices means tying patching activities to vulnerability remediation, regulatory requirements, and audit readiness. Documentation, traceability, and cross-team collaboration transform patching from a task into a governance-driven capability.
Common Pitfalls and Practical Tips to Sustain Momentum
Even with a solid plan, teams can hit common pitfalls such as incomplete inventories, testing bottlenecks, or over-reliance on automation without safeguards. Early identification of these risks allows you to design effective mitigations before incidents occur.
Practical tips to maintain momentum include keeping an up-to-date asset map, enabling safe automation with guardrails, enforcing clear change control, and communicating patch windows to stakeholders. Regular reviews and tabletop exercises help sustain momentum and keep the program aligned with business needs.
Frequently Asked Questions
What are software patches and why are they important in patch management best practices?
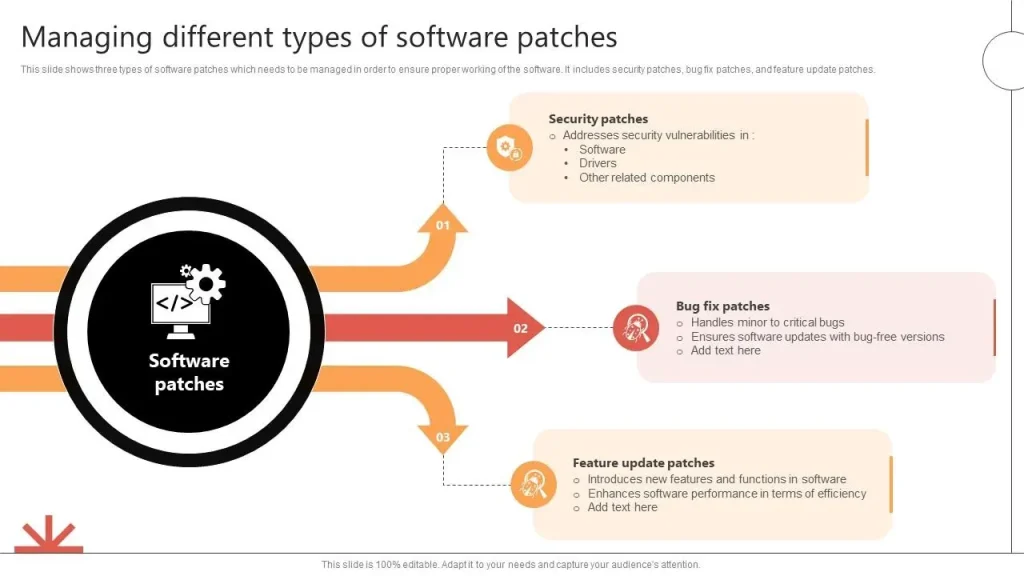
Software patches are vendor releases that fix vulnerabilities, bugs, and performance issues. Following patch management best practices, applying these updates reduces security risk, helps maintain compliance, and improves stability across endpoints, servers, and cloud workloads; this underscores the importance of software updates.
How can I manage patches effectively to minimize risk and downtime within my organization?
Adopt a patch management lifecycle: build an up-to-date inventory, perform vulnerability assessment, test patches in a staging environment, deploy in phased or scheduled waves, and verify success with auditing. This is how to manage patches effectively while balancing risk and operational load.
What is a good patching cadence and how should schedules be set for software patches?
A predictable cadence—commonly monthly—paired with a separate process for critical or zero-day patches helps teams plan testing and maintenance windows. Keep stakeholders informed and apply patches consistently to reduce exposure.
How do automated software updates fit into patch management best practices?
Automation speeds discovery, testing, deployment, and reporting and is a core component of patch management best practices. Use automation with safeguards such as pre-deployment checks, automated rollback, and appropriate approvals to avoid unintended impacts.
Why is testing and staging a critical part of the patch management lifecycle in software patches?
Testing in a staging environment that mirrors production helps catch compatibility issues before deployment, reducing risk and downtime. It supports safer, faster rollout and aligns with patch management best practices.
How do I measure success and demonstrate the importance of software updates in patch management?
Track metrics such as patch coverage, deployment time, success/failure rates, rollback frequency, and audit results. These indicators show adherence to patch management best practices and the real-world value of software patches.
| Area | Key Points | Impact / Why It Matters |
|---|---|---|
| Introduction |
|
Establishes the importance of patching and sets expectations for a proactive approach. |
| What are Software patches and Why They Matter |
|
Reduces risk, strengthens compliance posture, and supports stable, compatible environments across endpoints, servers, and cloud workloads. |
| The Patch Management Lifecycle |
|
A structured lifecycle reduces risk, improves visibility, and makes patching more predictable and safe. |
| Best Practices for Patch Management |
|
Provides a repeatable process to reduce risk, improve security, and support compliance. |
| Automation and Tools: Enhancing Patch Management |
|
Increases speed and consistency while preserving governance, traceability, and risk control. |
| Common Pitfalls and How to Avoid Them |
|
Helps teams anticipate failures and implement safeguards to maintain control and trust in patch activity. |
| The Human Side: Training, Change Management, and Culture |
|
People and processes are critical to patch success beyond technology. |
| Case Scenarios: Real-World Value of Patches |
|
Demonstrates tangible security and reliability benefits of effective patch management. |
Summary
Software patches are more than routine updates; they are a disciplined, ongoing effort to safeguard systems, ensure compliance, and maintain performance across an organization. By implementing a structured patch management lifecycle, adopting best practices, and leveraging automation where appropriate, you can transform patching from a reactive burden into a strategic capability. Key outcomes include improved visibility, risk-based prioritization, tested deployments, and clear governance. This approach reduces patch-related downtime, closes critical vulnerabilities, and strengthens your security posture, resilience, and business continuity.